Company
Resources
Datasheet
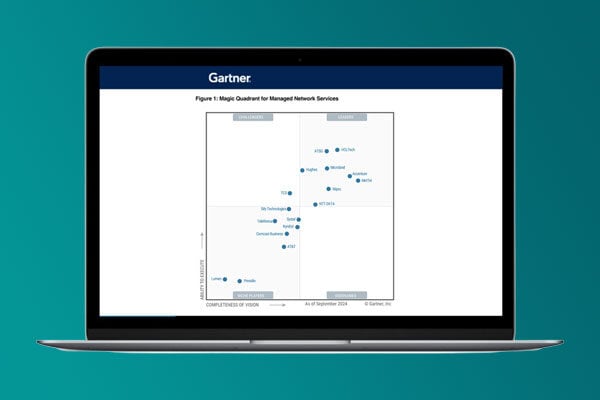
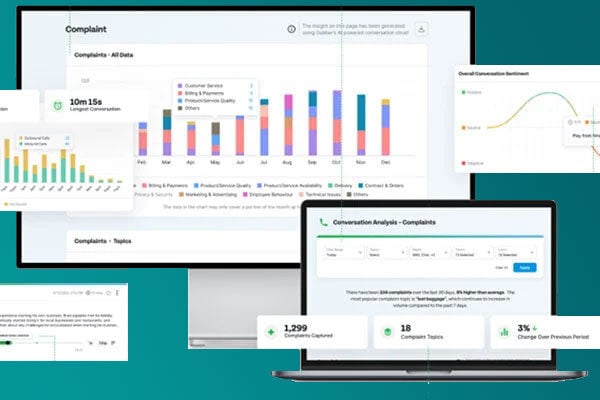
XTIUM Contact Suite: An Omnichannel Contact Center fully Unified with Microsoft Teams
View Asset >Case Study
XTIUM Contact Suite: An Omnichannel Contact Center fully Unified with Microsoft Teams
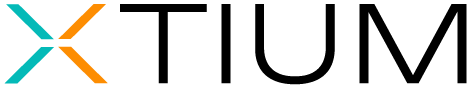
View Asset >Industry-recognized and certified to support your IT needs
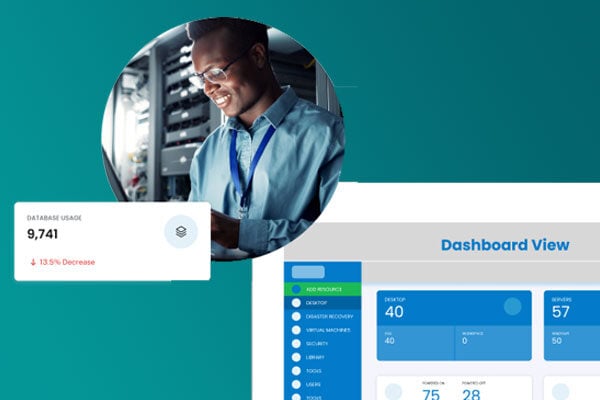
Trusted by 1,700+ mid-size and enterprise companies, we operate as an extension of your team—solving problems with urgency and accountability so you can focus on strategy, not firefighting. We are not just another MSP. We're your force multiplier that bring proven frameworks and real-world experience to help you secure, scale and streamline operations with fewer resources. Stop juggling vendors. Stop fighting uphill battles. Work with an IT partner who gets IT.