Post Call Survey
LEARN MORE
Resource Library
Join the ever-growing community of 2,559+ leaders in IT
- Insights that cut through the noise to understand what's effective.
- Sneak peeks of new strategies that other IT leaders (just like you) are using.
- Engaging interviews showcasing how others are managing their teams (and growing their own careers).
Looking for more information on our products and services? Welcome to Evolve IP's resource library. Here you'll find a variety of resources including white papers, webinars, case studies, data sheets, and more.
 [Contact Center as a Service]
[Contact Center as a Service]
Workforce Management
LEARN MOREContact Center Vendor Comparison
LEARN MOREBroadworks Call Center vs ECS Seat Comparison
LEARN MORECCI Health and Wellness Case Study
LEARN MOREUltimate Work From Home Checklist for Contact Center Professionals
LEARN MOREData Warehouse
LEARN MORECase Study: CCI Health and Wellness
LEARN MOREOpen Seating
LEARN MOREThe Evolve Contact Suite
LEARN MORECloud Interactive Voice Response (IVR)
LEARN MORECloud Dialer
LEARN MOREBroadSoft Success Story - JW Marriott Venice
LEARN MOREQueue Callback
LEARN MORE
 [Webex]
[Webex]
Evolve Anywhere with Webex
LEARN MOREEssential Guide for Collaboration Solutions
LEARN MORE
 [Microsoft Office]
[Microsoft Office]
Office 365 Deployment Checklist
LEARN MOREBackup for Office 365
LEARN MOREManaged Office 365
LEARN MORE
 [Teams]
[Teams]
Guide to Deploy Microsoft Teams with PBX
LEARN MOREMicrosoft Teams Benefits eBook
LEARN MORETeams TCO - Build vs Buy Calculator
LEARN MOREEvolve Anywhere with Microsoft Teams
LEARN MOREMicrosoft Teams Direct Routing Comparison
LEARN MOREMicrosoft Teams Voice Continuity Capabilities
LEARN MORE
 [Unified Communications and Collaboration]
[Unified Communications and Collaboration]
Unified Communications Vendor Comparison Matrix Evaluation
LEARN MORE2021 Remote Work Technology Survey
LEARN MOREVideo Conferencing Vendor Comparison Matrix
LEARN MOREUltimate Work From Home Checklist for Business Professionals
LEARN MORECall Recording with Voice AI
LEARN MORECase Study: Friedman LLC
LEARN MORECase Study: Ogletree Deakins
LEARN MOREEvolved Messaging
LEARN MORECRM Integration
LEARN MORECompany Overview
LEARN MOREEdge Compute, IoT, and Cloud Extension with Evolve IP Cloud Connect and SD-WAN
LEARN MOREAchieve the Perfect Network with Cloud Connect
LEARN MOREEmergency Services Frequently Asked Questions (FAQs)
LEARN MORECloud Fax
LEARN MOREUnified Communications Checklist
LEARN MORE
 [Virtual Desktops]
[Virtual Desktops]
Healthcare Case Study: Halfpenny Technologies
LEARN MOREDaaS Solutions Comparison Guide
LEARN MOREDisaster Recovery Checklist
LEARN MOREBusiness Continuity Checklist
LEARN MOREVeterinary Cloud Technology Case Study | Wellsboro Small Animal Hospital
LEARN MOREDesktop as a Service (DaaS)
LEARN MORECase Study: Johnson Investment Council Working Remotely
LEARN MOREWorkspaces: Comparing VDI to Hosted Virtual Desktops / DaaS
LEARN MOREMimecast Unified Email Management
LEARN MOREGartner Market Guide for DaaS
LEARN MOREManaged DaaS
LEARN MOREHybrid Workplace Survival Guide
LEARN MOREDesktop as a Service (DaaS) Vendor Comparison Matrix
LEARN MORESupercharge Workforce Mobility with Citrix DaaS
LEARN MORE5 Reasons your IT team needs Citrix DaaS
LEARN MOREThe future of IT security and hybrid work: Security without compromise
LEARN MOREThe Value of Virtualization
LEARN MOREOptimize VDI for the Future by Managing and Deploying your Desktop Services in the Cloud
LEARN MOREWhy Desktop as a Service?
LEARN MOREServiceMac, LLC Case Study
LEARN MOREVirtual Desktops for Remote Contact Center Agents
LEARN MOREHow to Choose a Desktop Delivery Model for the Digital Workplace
LEARN MORECalculating the True Cost of DaaS
LEARN MOREOld DaaS vs New DaaS
LEARN MOREZero Trust User Experience
LEARN MORECloud DaaS (Everything You Need To Know)
LEARN MOREHow financial services organizations can achieve security, flexibility, and greater efficiencies with virtualization
LEARN MOREModernizing financial services with Evolve IP Powered by Citrix
LEARN MORETypes of Virtual Desktop Offerings
LEARN MOREComparison Guide for Desktop as a Service Alternatives
LEARN MORE
 [Security]
[Security]
Remote Work Considerations Securing the New Corporate Network
LEARN MOREEvolve for Credit Unions
LEARN MORECase Study: US Dermatology Partners
LEARN MOREHealthcare Data Sheet
LEARN MOREDisaster Recovery Plan Template
LEARN MOREExecutive Guide to Implementing a Secure BYOD Policy
LEARN MOREModern Data Protection for Healthcare
LEARN MORETop 2022 Trends for Data Protection
LEARN MOREFive Best Practices for Cloud Security
LEARN MORESecurity Pitfalls of the "New Normal"
LEARN MOREUnlimited Backup as a Service (BaaS) for Microsoft 365 Data
LEARN MORE2022 Ransomware Trends Infographic
LEARN MORE2022 Ransomware Trends Report
LEARN MORENavigating the Journey to Work from Anywhere Securely
LEARN MOREYour essential IT ally for the enterprise hybrid workforce.



Simplify and future-proof your technology footprint with Evolve IP






It's nearly impossible to stay on top of every change in technology. Partner with Evolve IP and gain the combined experience of hundreds of technologists, all acting as an extension of your IT team. Helping you do more with less.























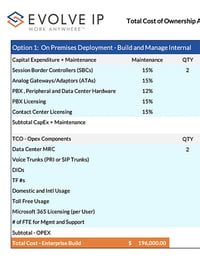

































.png?width=200&name=Calculating%20the%20True%20Cost%20of%20DaaS%20(1).png)
.png?width=200&name=Calculating%20the%20True%20Cost%20of%20DaaS%20(2).png)